Domain:
http://cnn.com
“The Cable News Network (CNN) is an American basic cable and satellite television channel that is owned by the Turner Broadcasting System division of Time Warner. The 24-hour cable news channel was founded in 1980 by American media proprietor Ted Turner. Upon its launch, CNN was the first television channel to provide 24-hour news coverage, and was the first all-news television channel in the United States. While the news channel has numerous affiliates, CNN primarily broadcasts from the Time Warner Center in New York City, and studios in Washington, D.C. and Los Angeles, its headquarters at the CNN Center in Atlanta is only used for weekend programming. CNN is sometimes referred to as CNN/U.S. to distinguish the American channel from its international sister network, CNN International. As of August 2010, CNN is available in over 100 million U.S. households. Broadcast coverage of the U.S. channel extends to over 890,000 American hotel rooms, as well as carriage on cable and satellite providers throughout Canada. Globally, CNN programming airs through CNN International, which can be seen by viewers in over 212 countries and territories. As of February 2015, CNN is available to approximately 96,289,000 cable, satellite and, telco television households (82.7% of households with at least one television set) in the United States.” (Wikipedia)
Discovered and Reported by:
Jing Wang, Division of Mathematical Sciences (MAS), School of Physical and Mathematical Sciences (SPMS), Nanyang Technological University (NTU), Singapore. (@justqdjing)
http://www.tetraph.com/wangjing/
Vulnerability Description:
CNN has a cyber security bug problem. It cab be exploited by XSS (Cross Site Scripting) and Open Redirect (Unvalidated Redirects and Forwards) attacks.
According to E Hacker News on June 06, 2013, (@BreakTheSec) came across a diet spam campaign that leverages the open redirect vulnerability in one of the top News organization CNN.
After the attack, CNN takes measures to detect Open Redirect vulnerabilities. The measure is quite good during the tests. Almost no links are vulnerable to Open Redirect attack on CNN’s website, now. It takes long time to find a new Open Redirect vulnerability that is un-patched on its website.
CNN.com was hacked by Open Redirect in 2013. While the XSS attacks happened in 2007.
<1> “The tweet apparently shows cyber criminals managed to leverage the open redirect security flaw in the CNN to redirect twitter users to the Diet spam websites.”
Figure from ehackingnews.com
At the same time, the cybercriminals have also leveraged a similar vulnerability in a Yahoo domain to trick users into thinking that the links point to a trusted website.
Yahoo Open Redirects Vulnerabilities:
http://securityrelated.blogspot.com/2014/12/yahoo-yahoocom-yahoocojp-open-redirect.html
Several other similar products 0-day vulnerabilities have been found by some other bug hunter researchers before. CNN has patched some of them. BugTraq is a full disclosure moderated mailing list for the *detailed* discussion and announcement of computer security vulnerabilities: what they are, how to exploit them, and how to fix them. The below things be posted to the Bugtraq list: (a) Information on computer or network related security vulnerabilities (UNIX, Windows NT, or any other). (b) Exploit programs, scripts or detailed processes about the above. (c) Patches, workarounds, fixes. (d) Announcements, advisories or warnings. (e) Ideas, future plans or current works dealing with computer/network security. (f) Information material regarding vendor contacts and procedures. (g) Individual experiences in dealing with above vendors or security organizations. (h) Incident advisories or informational reporting. (i) New or updated security tools. A large number of the fllowing web securities have been published here, Buffer overflow, HTTP Response Splitting (CRLF), CMD Injection, SQL injection, Phishing, Cross-site scripting, CSRF, Cyber-attack, Unvalidated Redirects and Forwards, Information Leakage, Denial of Service, File Inclusion, Weak Encryption, Privilege Escalation, Directory Traversal, HTML Injection, Spam. It also publishes suggestions, advisories, solutions details related to XSS and URL Redirection vulnerabilities and cyber intelligence recommendations.
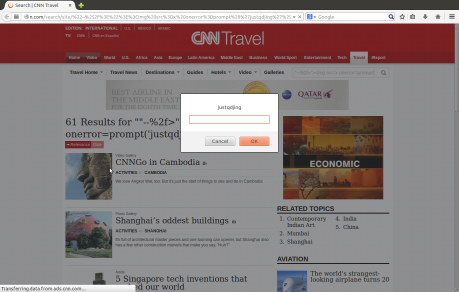
(1) CNN (cnn.com) Travel-City Related Links XSS (cross site scripting) Web Security Bugs
Domain:
travel.cnn.com/
Vulnerability Description:
The programming bug flaws occur at “/city/all” pages. All links under this URL are vulnerable to XSS attacks, e.g
XSS may allow a remote attacker to create a specially crafted request that would execute arbitrary script code in a user’s browser session within the trust relationship between their browser and the server. Base on Acunetix, exploited XSS is commonly used to achieve the following malicious results
- Identity theft
- Accessing sensitive or restricted information
- Gaining free access to otherwise paid for content
- Spying on user’s web browsing habits
- Altering browser functionality
- Public defamation of an individual or corporation
- Web application defacement
- Denial of Service attacks
PoC:
http://travel.cnn.com/city/all/all/tokyo/all‘ /”><img src=x onerror=prompt(/justqdjing/)>
http://travel.cnn.com/city/all/all/bangkok/all‘ /”><img src=x onerror=prompt(/justqdjing/)>
(1.1) Poc Video:
https://www.youtube.com/watch?v=Cu47XiDV38M&feature=youtu.be
(2) CNN cnn.com ADS Open Redirect Web Security Bug
Domain:
ads.cnn.com
Vulnerability Description:
The programming code flaw occurs at “event.ng” page with “&Redirect” parameter, i.e.
From OWASP, an open redirect is an application that takes a parameter and redirects a user to the parameter value without any validation. This vulnerability is used in phishing attacks to get users to visit malicious sites without realizing it. This could allow a user to create a specially crafted URL, that if clicked, would redirect a victim from the intended legitimate web site to an arbitrary web site of the attacker’s choosing. Such attacks are useful as the crafted URL initially appear to be a web page of a trusted site. This could be leveraged to direct an unsuspecting user to a web page containing attacks that target client side software such as a web browser or document rendering programs.
The vulnerabilities can be attacked without user login. Tests were performed on Microsoft IE (10.0.9200.16750) of Windows 8, Mozilla Firefox (34.0) & Google Chromium 39.0.2171.65-0 ubuntu0.14.04.1.1064 (64-bit) of Ubuntu (14.04),Apple Safari 6.1.6 of Mac OS X Lion 10.7.
(2.1) Use the following tests to illustrate the scenario painted above.
The redirected webpage address is “http://webcabinet.tumblr.com/“. Suppose that this webpage is malicious.
Vulnerable URL:
POC:
http://ads.cnn.com/event.ng/Type=click&FlightID=92160&AdID=125504&TargetID=1346&RawValues=&Redirect=http:%2f%2fwebcabinet.tumblr.com
Since CNN is well-known worldwide, this vulnerability can be used to do “Covert Redirect” attacks to other websites.
(2.1) Poc Video:
https://www.youtube.com/watch?v=FE8lhDvKGN0&feature=youtu.be
Those vulnerabilities were reported to CNN in early July by Contact from Here. But they are still not been patched yet.
http://edition.cnn.com/feedback/#cnn_FBKCNN_com
More Details:
http://seclists.org/fulldisclosure/2014/Dec/128
http://lists.openwall.net/full-disclosure/2014/12/29/6
http://permalink.gmane.org/gmane.comp.security.fulldisclosure/1395
http://static-173-79-223-25.washdc.fios.verizon.net/?l=full-disclosure
http://securitypost.tumblr.com/post/107868680057/ithut-cnn-cnn-com-travel
http://ittechnology.lofter.com/post/1cfbf60d_5500df0
http://ithut.tumblr.com/post/120833062743/cnn-xss-url-redirection-bug
http://www.tetraph.com/blog/it-news/cnn-xss-url-redirect-bug/
https://biyiniao.wordpress.com/2015/01/08/cnn-xss-open-redirect-bug/
http://whitehatpost.blog.163.com/blog/static/24223205420155613753998/
https://plus.google.com/u/0/+wangfeiblackcookie/posts/bFkukxiUfXK
https://www.facebook.com/permalink.php?story_fbid=674936469318135
http://tetraph.blogspot.com/2015/06/cnn-xss-redirect-bug.html
http://diebiyi.com/articles/news/cnn-xss-url-redirect-bug/
https://twitter.com/yangziyou/status/607060937309159425
https://redysnowfox.wordpress.com/2014/12/31/cnn-xss-url-redirect-bug/
https://www.facebook.com/permalink.php?story_fbid=1043534509019886
http://whitehatpost.lofter.com/post/1cc773c8_7338196
http://securityrelated.blogspot.com/2014/12/cnn-cnncom-travel-xss-and